Banks: Card Breach at Some Chick-fil-A’s
mardi 30 décembre 2014 à 23:25Sources at several U.S. financial institutions say they have traced a pattern of credit card fraud back to accounts that all were used at different Chick-fil-A fast food restaurants around the country. Chick-fil-A told KrebsOnSecurity that it has received similar reports and is working with IT security firms and law enforcement in an ongoing investigation.
KrebsOnSecurity first began hearing from banks about possible compromised payment systems at Chick-fil-A establishments in November, but the reports were spotty at best. Then, just before Christmas, one of the major credit card associations issued an alert to several financial institutions about a breach at an unnamed retailer that lasted between Dec. 2, 2013 and Sept. 30, 2014.
One financial institution that received that alert said the bank had nearly 9,000 customer cards listed in that alert, and that the only common point-of-purchase were Chick-fil-A locations.
“It’s crazy because 9,000 customer cards is more than the total number of cards we had impacted in the Target breach,” the banking source said, speaking on condition of anonymity.
The source said his institution saw Chick-fil-A locations across the country impacted, but that the bulk of the fraud seemed concentrated at locations in Georgia, Maryland, Pennsylvania, Texas and Virginia.
Reached for comment about the findings, Chick-fil-A issued the following statement:
“Chick-fil-A recently received reports of potential unusual activity involving payment cards used at a few of our restaurants. We take our obligation to protect customer information seriously, and we are working with leading IT security firms, law enforcement and our payment industry contacts to determine all of the facts.”
“We want to assure our customers we are working hard to investigate these events and will share additional facts as we are able to do so. If the investigation reveals that a breach has occurred, customers will not be liable for any fraudulent charges to their accounts — any fraudulent charges will be the responsibility of either Chick-fil-A or the bank that issued the card. If our customers are impacted, we will arrange for free identity protection services, including credit monitoring.”
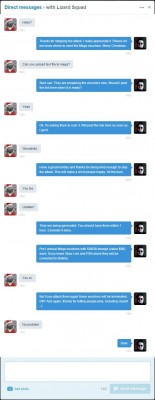
My suspicion is that — if confirmed — this breach will be found to have impacted only a subset of Chick-fil-A’s 1,850 locations in 41 states and the District of Columbia. In that respect, it would be much like the breaches first reported in this blog earlier this year at other fast food chains — Dairy Queen and Jimmy Johns. In both of those breaches, the stores impacted were franchises that outsourced the management of their point-of-sale systems to specific third party companies.
In September, KrebsOnSecurity reported that a different hacked point-of-sale provider was the driver behind a breach that impacted more than 330 Goodwill locations nationwide. That breach, which targeted payment vendor C&K Systems Inc., persisted for 18 months, and involved two other as-yet unnamed C&K customers.
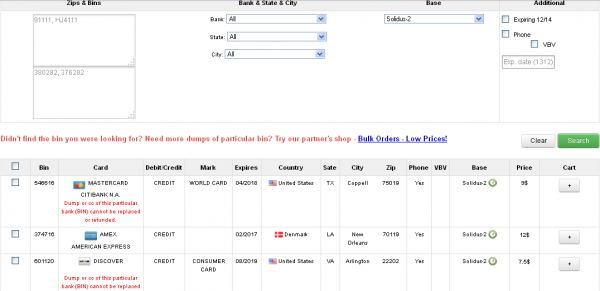
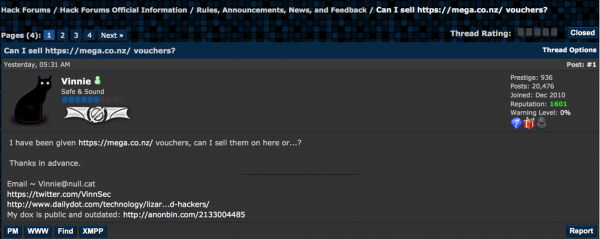
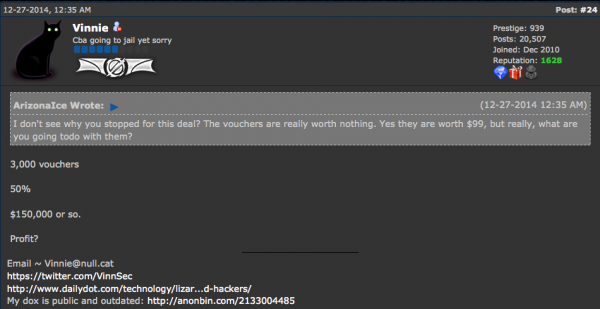
In all of these incidents, the intruders managed to install malicious software on point-of-sale systems at the affected merchants. Point-of-sale malware, like the malware that hit C&K as well as Target, Home Depot, Neiman Marcus and other retailers this past year, is designed to steal the data encoded onto the magnetic stripe on the backs of debit and credit cards. This data can be used to create counterfeit cards, which are then typically used to purchase physical goods at big-box retailers.
Point-of-sale compromises have come to define 2014. Earlier this year, the U.S. Secret Service issued an advisory that a point-of-sale malware strain known as “Backoff” had struck more than 1,000 U.S. companies since Oct. 2013.
Companies that suffer credit card breaches offer credit monitoring services as a means of placating nervous customers, but bear in mind that credit monitoring services do nothing to prevent fraud on existing accounts (such as credit cards you may have in your wallet). There is no substitute for monitoring your monthly bank and credit card statements for unauthorized or suspicious transactions.
If, on the other hand, you’re looking for more information on credit monitoring services, or for tips about how to protect yourself and loved ones from identity thieves, please check out this article.