John Clifton Davies, a 60-year-old con man from the United Kingdom who fled the country in 2015 before being sentenced to 12 years in prison for fraud, has enjoyed a successful life abroad swindling technology startups by pretending to be a billionaire investor. Davies’ newest invention appears to be “CodesToYou,” which purports to be a “full cycle software development company” based in the U.K.

The scam artist John Bernard a.k.a. Alan John Mykailov (left) in a recent Zoom call, and a mugshot of John Clifton Davies from nearly a decade earlier.
Several articles here have delved into the history of John Bernard, the pseudonym used by a fake billionaire technology investor who tricked dozens of startups into giving him tens of millions of dollars.
John Bernard’s real name is John Clifton Davies, a convicted fraudster from the United Kingdom who is currently a fugitive from justice. For several years until reinventing himself again quite recently, Bernard pretended to be a billionaire Swiss investor who made his fortunes in the dot-com boom 20 years ago.
“The Private Office of John Bernard” let it be known to investment brokers that he had tens of millions of dollars to invest in tech startups, and he attracted a stream of new victims by offering extraordinarily generous finder’s fees to brokers who helped him secure new clients. But those brokers would eventually get stiffed because Bernard’s company would never consummate a deal.

John Bernard’s former website, where he pretended to be a billionaire tech investor.
Bernard would promise to invest millions in tech startups, and then insist that companies pay tens of thousands of dollars worth of due diligence fees up front. However, the due diligence company he insisted on using — another Swiss firm called The Inside Knowledge GmbH — also was secretly owned by Bernard, who would invariably pull out of the deal after receiving the due diligence money.
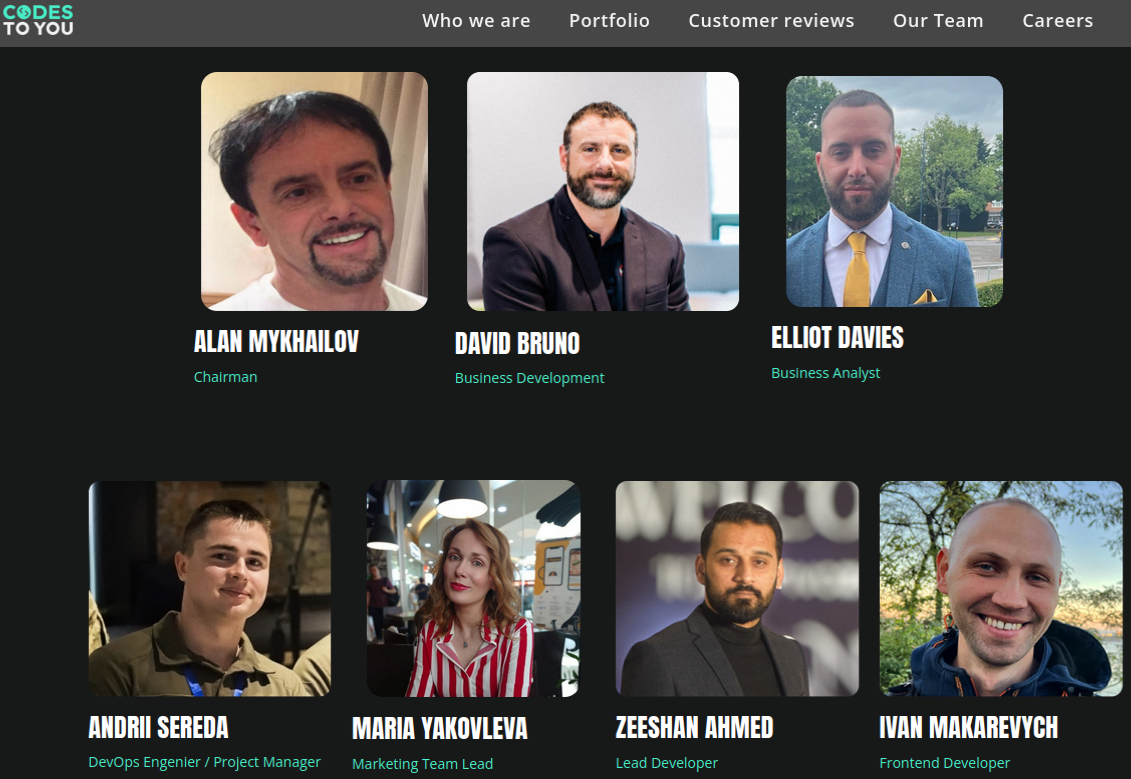
A variety of clues suggest Davies has recently adopted at least one other identity — Alan John Mykhailov — who is listed as chairman of a British concern called CodesToYou LTD, incorporated in May 2022. The CodesToYou website says the company employs talented coders in several countries, and that its programmers offer “your ultimate balance between speed, cost and quality.”
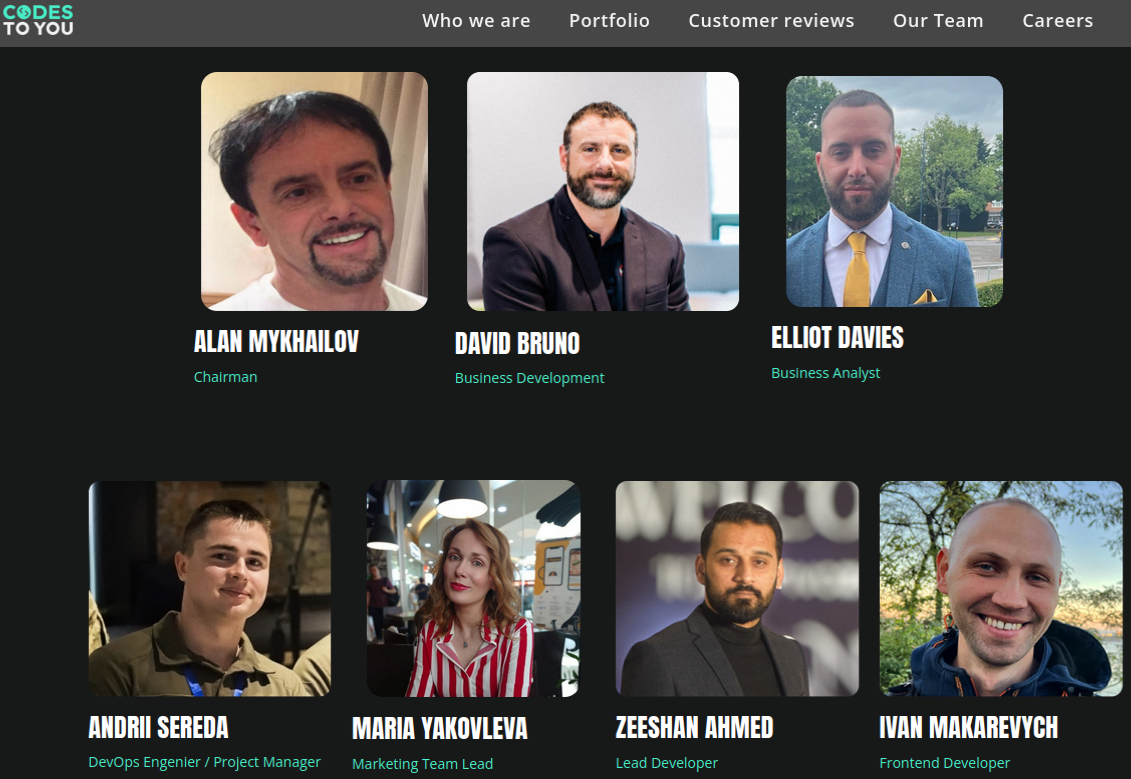
The team from CodesToYou.
In response to questions from KrebsOnSecurity, CodesToYou’s marketing manager — who gave their name only as “Zhena” — said the company was not affiliated with any John Bernard or John Clifton Davies, and maintained that CodesToYou is a legitimate enterprise.
But publicly available information about this company and its leadership suggests otherwise. Official incorporation documents from the U.K.’s Companies House represent that CodesToYou is headed by an Alan John Mykhailov, a British citizen born in March 1958.
Companies House says Mykhailov is an officer in three other companies, including one called Blackstone Corporate Alliance Ltd. According to the Swiss business tracking service business-monitor.ch, Blackstone Corporate Alliance Ltd. is currently the entity holding a decision-making role in John Bernard’s fake due diligence company — The Inside Knowledge GmbH — which is now in liquidation.
A screen shot of the stock photos and corporate-speak on John Bernard’s old website. Image: Archive.org
Also listed as a partner in Blackstone Corporate Alliance Limited is Igor Hubskyi (a.k.a. Igor Gubskyi), a Ukrainian man who was previously president of The Inside Knowledge GmbH.
The CodesToYou website says the company’s marketing team lead is Maria Yakovleva, and the photo of this employee matches the profile for the LinkedIn account name “Maria Y.” That same LinkedIn profile and photo previously listed Maria by a different first and last name — Mariya Kulikova; back then, Ms. Kulikova’s LinkedIn profile said she was an executive assistant in The Private Office of Mr. John Bernard.
Companies House lists Alan John Mykhailov as a current officer in two other companies, including Frisor Limited, and Ardelis Solutions Limited. A cached copy of the now-defunct Ardelis Solutions website says it was a private equity firm.
CodesToYou’s Maria also included Ardelis Solutions in the work history section of her LinkedIn resume. That is, until being contacted by this author on LinkedIn, after which Maria’s profile picture and any mention of Ardelis Solutions were deleted.
Listed as head of business development at CodesToYou is David Bruno, a Canadian man whose LinkedIn profile says he is founder of an organization called “World Privacy Resource.” As KrebsOnSecurity reported in 2020, Bruno was at the time promoting himself as the co-CEO of a company called SafeSwiss Secure Communication AG, and the founder of another tech startup called Secure Swiss Data.
Secure Swiss Data’s domain — secureswissdata.com — is a Swiss concern that sells encrypted email and data services. According to DomainTools.com, that website name was registered in 2015 by The Inside Knowledge GmbH. In February 2020, a press release announced that Secure Swiss Data was purchased in an “undisclosed multimillion buyout” by SafeSwiss Secure Communication AG.
A cached copy of the Ardelis Solutions website, which said it was a private equity firm and included similar stock images as John Bernard’s investment website.
When reached in 2020 and asked about his relationship to Mr. Bernard, Mr. Bruno said the two were business partners and that he couldn’t imagine that Mr. Bernard would be involved in anything improper. To this day Mr. Bruno is the only person I’ve spoken to who has had anything positive to say about Mr. Bernard.
Mr. Bruno did not respond to requests for comment this time around, but his LinkedIn profile no longer makes any mention of Secure Swiss Data or SafeSwiss — both companies he claimed to run for many years. Nor does it mention CodesToYou. However, Mr. Bruno’s former company SafeSwiss is listed as one of the six “portfolio” companies whose services are promoted on the CodesToYou website.
In mid-2021, Bruno announced he was running for public office in Ontario.
“The Kenora resident is no stranger to the government as he contributed to Canada’s new Digital Charter, Bill C-11, which is a new Cyber Security policy,” reported Drydennow.com, a news website that covers Northwestern Ontario. Drydennow says the next federal election is expected to be held on or before Oct. 16, 2023.
John Clifton Davies was convicted in 2015 of swindling businesses throughout the U.K. that were struggling financially and seeking to restructure their debt. For roughly six years, Davies ran a series of firms that pretended to offer insolvency services, but instead simply siphoned what little remaining money these companies had.
The very first entity mentioned in the technology portfolio advertised on the CodesToYou website is called “MySolve,” and it purports to offer a “multi-feature platform for insolvency practitioners.”
Mr. Davies’ fourth wife, Iryna Davies, is listed as a director of one of the insolvency consulting businesses in the U.K. that was part of John Davies’ 2015 fraud conviction. Prior to his trial for fraud, Davies served 16 months in jail before being cleared of murdering his third wife on their honeymoon in India: Colette Davies, 39, died after falling 80 feet from a viewing point at a steep gorge in the Himachal Pradesh region of India.
Mr. Davies was charged with murder and fraud after he attempted to collect GBP 132,000 in her life insurance payout, but British prosecutors ultimately conceded they did not have enough evidence to convict him.
The scams favored by Davies and his alter egos are smart because he never approaches investors directly; rather, investors are incentivized to put his portfolio in front of tech firms seeking financial backing. And all the best cons begin as an idea or possibility planted in the target’s mind.
It’s also a reliable scam because companies bilked by small-time investment schemes rarely pursue legal action, mainly because the legal fees involved can quickly surpass the losses. On top of that, many victims will likely be too ashamed to admit their duping. Victims who do press their case in court and win then face the daunting challenge of collecting damages from a slew of ephemeral shell corporations.
The latest Bernard victim to speak publicly — a Norwegian company hoping to build a fleet of environmentally friendly shipping vessels — is now embroiled in a lawsuit over a deal gone bad. As part of that scam, Bernard falsely claimed to have secured $100 million from six other wealthy investors, including the founder of Uber and the artist Abel Makkonen Tesfaye, better known as The Weeknd.