Firms Could Be Forced to Disgorge Profits from Tax Refund Fraud
mardi 9 juin 2015 à 14:03Last week, KrebsOnSecurity ran an interview with Julie Magee, Alabama’s chief tax administrator, to examine what the states are doing in tandem with the IRS and others to make it harder for ID thieves to commit tax refund fraud — a $6 billion a year problem. Today we’ll hear from John Valentine, chair of Utah’s State Tax Commission, about the challenges his state faced this year, as well as the prospect that tax preparation firms could be forced return to the U.S. Treasury any profits they make from processing fraudulent tax refunds.
 Valentine was a tax attorney before being appointed the chair of Utah’s tax commission, so he’s familiar with the challenges facing both the tax preparation industry as well as the tax agencies.
Valentine was a tax attorney before being appointed the chair of Utah’s tax commission, so he’s familiar with the challenges facing both the tax preparation industry as well as the tax agencies.
“I came out of the private sector and spent nearly 40 years suing the state tax commission and the IRS,” Valentine said. “Now I am that.”
Utah is actively engaged in an IRS task force made up of state, federal and industry tax experts trying to quash refund fraud. Like Alabama’s deputy tax commissioner Joe Garrett — who had a $7,700 fraudulent refund filed in his name — several of Utah’s senior tax administration officials also were victimized by ID thieves this year.
“We’ve had some of our senior people who had tax returns filed on their behalf,” Valentine said. “Of course, they had not filed them yet and we knew that they were more than a little suspicious.”
Among the steps the task force is considering is whether to mail all taxpayers an Identity Protection Personal Identification Number (IP PIN) that is tied to each taxpayer and must be included in each tax return. The IRS issues the IP PINs to taxpayers who have suffered tax return fraud. Additionally, consumers willing to swear they have been victims of identity theft can apply for a filing PIN, however the IRS is picky about granting those requests.
Even if the IRS were to switch to issuing IP PINs to all taxpayers, the agency would still run up against the thorny problem of how to verify consumers’ identity (no doubt, that challenge would be exacerbated by millions of taxpayers phoning the IRS after losing or misplacing their assigned PINs). A major focus of the working groups attention is finding better ways to authenticate people beyond merely requesting static identifiers (Social Security numbers, dates of birth) and other data that is frequently exposed in data breaches and is readily for sale on underground markets.
“They’re going to have to switch to a 2-factor authentication system, where they really strengthen the front-end of that authentication,” Valentine said of the tax preparation firms like TurboTax, which briefly shut down all state tax filing this year after a massive spike in phony refund requests put through its systems via hijacked and fraudulently created TurboTax accounts.
Valentine also made the decision to halt all Utah tax refunds around that same time.
“When we installed our [anti-fraud] analytics program, we thought we were getting a lot of false positives, so we did a bunch of back checking,” he said “While we were doing that, I made a decision to stop all refunds. For a period of two weeks Utah gave no refunds while we worked through the analytics to make sure we’d identified the nature and extent of the fraud. It turned out to be much more extensive than we’ve ever seen.”
In fact, ten times as much as any year prior, according to Valentine.
“We’ve always seen fraud where a tax practitioner will file a whole bunch of fraudulent returns, or we’ll see ID theft targeting a large employer. But this fraud wave was a little tougher, because it went across spectrum of employers, across the entire demographic of taxpayers, high low and middle income. Also, the fraud wasn’t regionalized — it was across the whole state — and [the fraudsters] didn’t seem to be selective as to who they hit. They got people of notoriety and people nobody knew. In the end, it appeared that the common factor among all of them was how you filed in 2013,” because the phony 2014 returns all included nearly identical information as the victim’s 2013 returns.
“What we saw in Utah was a population of the same information in the 2013 return into the 2014 return, with the exception of bank routing and bank account number,” Valentine said. “That’s a different fraud that we’d just never seen before.”
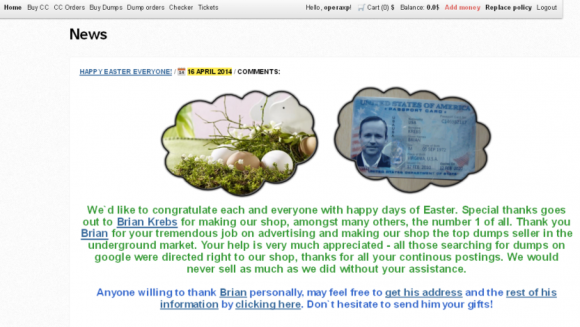
TurboTax’s lax security around authentication for new and existing accounts played a well-documented role in the type of fraud described by Valentine this year. But ID thieves also got help directly from the IRS this year. Late last month, the agency suspended the “get transcript” function that previously allowed taxpayers to order a copy of their previous year’s W2 information, among other data; turns out, crooks had used the service to pull tax data on more than 100,000 citizens, stealing tens of millions from the U.S. Treasury in the process.
PREPAID MADNESS
In March, Valentine testified on Capitol Hill on the tax fraud issue, and he urged lawmakers to change the way prepaid cards are numbered so that banks and tax administrators can more easily block or filter refunds destined for prepaid debit cards — the money laundering vehicle of choice for virtually all fraudulent refund requests.
Prepaids are notoriously easy for crooks to use for tax fraud because the process for opening a new prepaid and using it to receive funds can be done anonymously, unlike opening a new checking account at a local bank branch. When the refunds get deposited to prepaids, crooks can then very easily and anonymously use them as cash or to withdraw money at ATMs.
“The process for opening a prepaid debit card appears to be very easy,” Valentine said. “The normal ‘know your customer’ rules [that banks typically are required to follow] appear to be glossed over with this industry.”
Specifically, Valentine proposed modifying the routing number on prepaid cards so that the cards would be more easily distinguishable from debit cards attached to actual checking and savings accounts. Valentine said his suggestion was followed by many head nods by lawmakers in the committee hearing, but so far there doesn’t appear to have been any movement to change the status quo.
And that inertia seems to suit the prepaid card industry just fine. Brad Fauss, interim executive director and general counsel of the Network Branded Prepaid Card Association, said
the NBPCA believes that the key to solving identity theft tax refund fraud is to attack the problem at its source – where the identification credentials are compromised – rather than focusing on the method of disbursement after the fraud has occurred.
“Separately tracking routing and transit numbers, or RTNs, for prepaid accounts is impractical because financial institutions often use the same RTN’s for multiple banking products, such as checking accounts and prepaid cards, and fundamentally falls short since it will not stop fraud but will only prompt fraudsters to utilize alternative disbursement vehicles,” Fauss said.
Nevertheless, tax return fraud could become a dicey legal and financial quagmire for banks, tax preparation firms and prepaid card providers, each of which charge hefty fees for processing such transactions (see this story for a breakdown of how these companies are profiting from refund fraud).
Asked whether he was aware of anyone urging or requiring financial and tax providers to disgorge profits from tax refunds they process that turn out to be fraudulent, the formerly litigious tax attorney said these firms should be very concerned about that risk.
“I’m not aware of anyone calling for that, no, but under general principles of law, that’s one that would be a normal recourse,” he said. “Coming from the private sector, that would be the type of thing you would normally expect to see someone asserting. If I were general counsel for these third-party vendors, I would be saying, ‘Man, we run exposure here for disgorgement of fees that were from fraudulent returns, so we’ve got to clean this up right away.’”



![One of countless pages archived from Kallysky[dot]com](./media/622f5cee.kallysecrets-580x480.png)