Security Firm Redefines APT: African Phishing Threat
mercredi 20 mai 2015 à 06:32A security firm made headlines earlier this month when it boasted it had thwarted plans by organized Russian cyber criminals to launch an attack against multiple US-based banks. But a closer look at the details behind that report suggests the actors in question were relatively unsophisticated Nigerian phishers who’d simply registered a bunch of new fake bank Web sites.
The report was released by Colorado Springs, Colo.-based security vendor root9B, which touts a number of former National Security Agency (NSA) and Department of Defense cybersecurity experts among its ranks. The report attracted coverage by multiple media outlets, including, Fox News, Politico, SC Magazine and The Hill. root9B said it had unearthed plans by a Russian hacking gang known variously as the Sofacy Group and APT28. APT is short for “advanced persistent threat,” and it’s a term much used among companies that sell cybersecurity services in response to breaches from state-funded adversaries in China and Russia that are bent on stealing trade secrets via extremely stealthy attacks.
“While performing surveillance for a root9B client, the company discovered malware generally associated with nation state attacks,” root9B CEO Eric Hipkins wrote of the scheme, which he said was targeted financial institutions such as Bank of America, Regions Bank and TD Bank, among others.
“It is the first instance of a Sofacy or other attack being discovered, identified and reported before an attack occurred,” Hipkins said. “Our team did an amazing job of uncovering what could have been a significant event for the international banking community. We’ve spent the past three days informing the proper authorities in Washington and the UAE, as well as the CISOs at the financial organizations.”
However, according to an analysis of the domains reportedly used by the criminals in the planned attack, perhaps root9B should clarify what it means by APT. Unless the company is holding back key details about their research, their definition of APT can more accurately be described as “African Phishing Threat.”
The report correctly identifies several key email addresses and physical addresses that the fraudsters used in common across all of the fake bank domains. But root9B appears to have scant evidence connecting the individual(s) who registered those domains to the Sofacy APT gang. Indeed, a reading of their analysis suggests their sole connection is that some of the fake bank domains used a domain name server previously associated with Sofacy activity: carbon2u[dot]com (warning: malicious host that will likely set off antivirus alerts).
The problem with that linkage is although carbon2go[dot]com was in fact at one time associated with activity emanating from the Sofacy APT group, Sofacy is hardly the only bad actor using that dodgy name server. There is plenty of other badness unrelated to Sofacy that calls Carbon2go home for their DNS operations, including these clowns.
From what I can tell, the vast majority of the report documents activity stemming from Nigerian scammers who have been conducting run-of-the-mill bank phishing scams for almost a decade now and have left quite a trail.
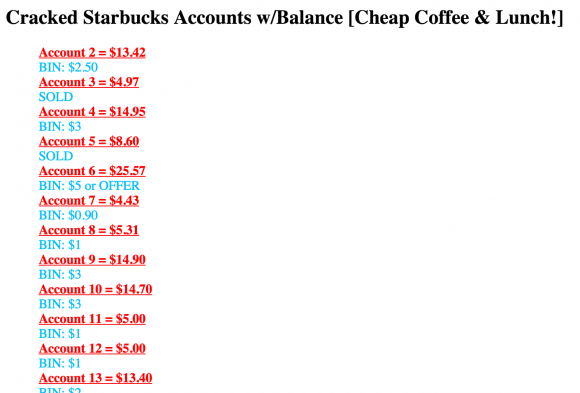
 For example, most of the wordage in this report from root9B discusses fake domains registered to a handful of email addresses, including “adeweb2001@yahoo.com,” adeweb2007@yahoo.com,” and “rolexzad@yahoo.com”.
For example, most of the wordage in this report from root9B discusses fake domains registered to a handful of email addresses, including “adeweb2001@yahoo.com,” adeweb2007@yahoo.com,” and “rolexzad@yahoo.com”.
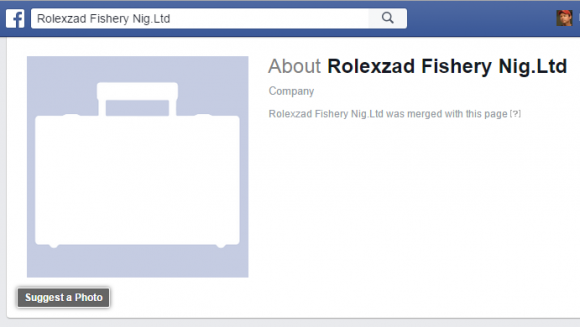
Each of these emails have long been associated with phishing sites erected by apparent Nigerian scammers. They are tied to this Facebook profile for a Showunmi Oluwaseun, who lists his job as CEO of a rather fishy-sounding organization called Rolexzad Fishery Nig. Ltd.
The domain rolexad[dot]com was flagged as early as 2008 by aa419.org, a volunteer group that seeks to shut down phishing sites — particularly those emanating from Nigerian scammers (hence the reference to the Nigerian criminal code 419, which outlaws various confidence scams and frauds). That domain also references the above-mentioned email addresses. Here’s another phishy bank domain registered by this same scammer, dating all the way back to 2005!
Bob Zito, a spokesperson for root9B, said “the team stands by the report as 100 percent accurate and it has been received very favorably by the proper authorities in Washington (and others in the cyber community, including other cyber firms).”
I wanted to know if I was alone in finding fault with the root9B report, so I reached out to Jaime Blasco, vice president and chief scientist at AlienVault — one of the security firms that first published the initial findings on the Sofacy/APT28 group back in October 2014. Blasco called the root9B research “very poor” (full disclosure: AlienVault is one of several advertisers on this blog).
“Actually, there isn’t a link between what root9B published and Sofacy activity,” he said. “The only link is there was a DNS server that was used by a Sofacy domain and the banking stuff root9B published. It doesn’t mean they are related by any means. I’m really surprised that it got a lot of media attention due to the poor research they did, and [their use] of [terms] like ‘zeroday hashes’ in the report really blew my mind. Apart from that it really looks like a ‘marketing report/we want media coverage asap,’ since days after that report they published their Q1 financial results and probably that increased the value of their penny stocks.”
Blasco’s comments may sound harsh, but it is true that root9B Chairman Joe Grano bought large quantities of the firm’s stock roughly a week before issuing this report. On May 14, 2015, root9B issued its first quarter 2015 financial results.
There is an old adage: If the only tool you have is a hammer, you tend to treat everything as if it were a nail. In this case, if all you do is APT research, then you’ll likely see APT actors everywhere you look.