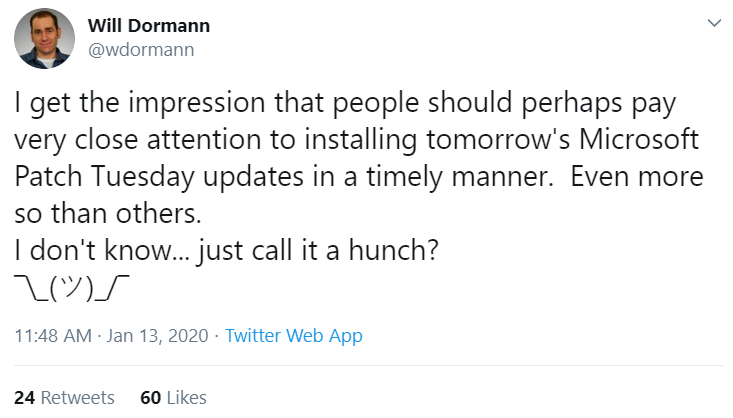
Microsoft today released updates to plug 50 security holes in various flavors of Windows and related software. The patch batch includes a fix for a flaw in Windows 10 and server equivalents of this operating system that prompted an unprecedented public warning from the U.S. National Security Agency. This month also marks the end of mainstream support for Windows 7, a still broadly-used operating system that will no longer be supplied with security updates.
 As first reported Monday by KrebsOnSecurity, Microsoft addressed a severe bug (CVE-2020-0601) in Windows 10 and Windows Server 2016/19 reported by the NSA that allows an attacker to spoof the digital signature tied to a specific piece of software. Such a weakness could be abused by attackers to make malware appear to be a benign program that was produced and signed by a legitimate software company.
As first reported Monday by KrebsOnSecurity, Microsoft addressed a severe bug (CVE-2020-0601) in Windows 10 and Windows Server 2016/19 reported by the NSA that allows an attacker to spoof the digital signature tied to a specific piece of software. Such a weakness could be abused by attackers to make malware appear to be a benign program that was produced and signed by a legitimate software company.
An advisory (PDF) released today by the NSA says the flaw may have far more wide-ranging security implications, noting that the “exploitation of the vulnerability allows attackers to defeat trusted network connections and deliver executable code while appearing as legitimately trusted entities.”
“NSA assesses the vulnerability to be severe and that sophisticated cyber actors will understand the underlying flaw very quickly and, if exploited, would render the previously mentioned platforms as fundamentally vulnerable,” the advisory continues. “The consequences of not patching the vulnerability are severe and widespread.”
Matthew Green, an associate professor in the computer science department at Johns Hopkins University, said the flaw involves an apparent implementation weakness in a component of recent Windows versions responsible for validating the legitimacy of authentication requests for a panoply of security functions in the operating system.
Green said attackers can use this weakness to impersonate everything from trusted Web sites to the source of software updates for Windows and other programs.
“Imagine if I wanted to pick the lock in your front door,” Green analogized. “It might be hard for me to come up with a key that will open your door, but what if I could tamper with or present both the key and the lock at the same time?”
Kenneth White, security principal at the software company MongoDB, equated the vulnerability to a phone call that gets routed to a party you didn’t intend to reach.
“You pick up the phone, dial a number and assume you’re talking to your bank or Microsoft or whomever, but the part of the software that confirms who you’re talking to is flawed,” White said. “That’s pretty bad, especially when your system is saying download this piece of software or patch automatically and it’s being done in the background.”
Both Green and White said it likely will be a matter of hours or days before security researchers and/or bad guys work out ways to exploit this bug, given the stakes involved. Indeed, already this evening KrebsOnSecurity has seen indications that people are teasing out such methods, which will likely be posted publicly online soon.
According to security vendor Qualys, only eight of the 50 flaws fixed in today’s patch roundup from Microsoft earned the company’s most dire “critical” rating, a designation reserved for bugs that can be exploited remotely by malware or miscreants to seize complete control over the target computer without any help from users.
Once again, some of those critical flaws include security weaknesses in the way Windows implements Remote Desktop connections, a feature that allows systems to be accessed, viewed and controlled as if the user was seated directly in front of the remote computer. Other critical patches include updates for the Web browsers and Web scripting engines built into Windows, as well as fixes for ASP.NET and the .NET Framework.
The security fix for the CVE-2020-0601 bug and others detailed in this post will be offered to Windows users as part of a bundle of patches released today by Microsoft. To see whether any updates are available for your Windows computer, go to the Start menu and type “Windows Update,” then let the system scan for any available patches.
Keep in mind that while staying up-to-date on Windows patches is a must, it’s important to make sure you’re updating only after you’ve backed up your important data and files. A reliable backup means you’re not losing your mind when the odd buggy patch causes problems booting the system. So do yourself a favor and backup your files before installing any patches. Windows 10 even has some built-in tools to help you do that, either on a per-file/folder basis or by making a complete and bootable copy of your hard drive all at once.
Today also marks the last month in which Microsoft will ship security updates for Windows 7 home/personal users. I count myself among some 30 percent of Windows users who still like and (ab)use this operating system in one form or another, and am sad that this day has come to pass. But if you rely on this OS for day-to-day use, it’s probably time to think about upgrading to something newer.
That might be a computer with Windows 10. Or maybe you have always wanted that shiny MacOS computer. If cost is a primary motivator and the user you have in mind doesn’t do much with the system other than browsing the Web, perhaps a Chromebook or an older machine with a recent version of Linux is the answer. Whichever system you choose, it’s important to pick one that fits the owner’s needs and provides security updates on an ongoing basis.
As always, if you experience glitches or problems installing any of these patches this month, please consider leaving a comment about it below; there’s a better-than-even chance other readers have experienced the same and may chime in here with some helpful tips.


 As
As